Is Cloud Computing the Ideal Future for Internet?
3 min read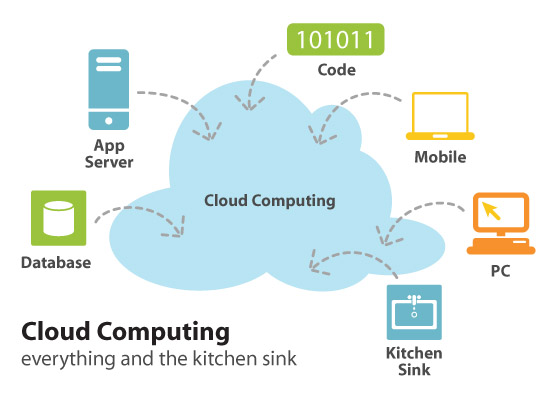
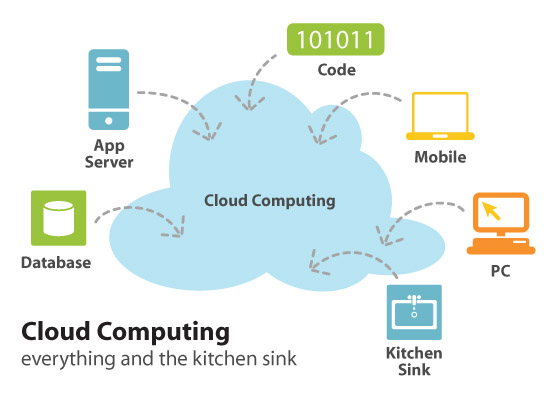
Cloud computing has experienced rapid growth lately; however, there are doubts about it. Jonathan Strickland of ‘How Stuff Works’, says Cloud computing uses different IT resources that are provided as a service through a network, i.e. the internet, making them available to users via a web browser or a desktop or mobile application. All user data and software used by businesses are preserved in isolated servers, resulting in greater application-running speed, better control and less upkeep, while at the same time enabling businesses to meet unexpected increases in demand.
According to Strickland, cloud computing is a preferred alternative to providing every member of the organization with a computer, which increases costs. This eliminates the need to equip every computer with the required software, allowing employees to access a web-based facility accommodating all the programs through a single application.
Services like Gmail and Hotmail are also based on the concept of cloud, thus it is very much likely that you have used cloud before. Instead of logging-in to your e-mail account through your computer, you access the account privately, and all the data and software are present on the cloud.
There are two parts of a cloud computing setup: the front-end and the back-end, interconnected by means of a network, such as the internet. The front end is the part that is visible to the end-users, while the back-end unit comprises of different servers, computers and data structures.
As stated by Eric Knorr, the finest cloud computing solutions are offered by software as a service (SaaS) providers, using a browser to provide a single application to multiple users. This does not require any investment from consumers in servers and in acquiring software licenses, and reduces maintenance costs of the provider.
Although cloud computing is becoming immensely popular in IT services and results in lower costs, privacy remains a big issue in this regard, according to Leslie Cauley of USA Today. The simplicity of communication and data storage between the user and service provider can prove to be a disadvantage in some cases.
There have been several occurrences such as “NSA program”, collaborating with AT&T and Verizon to record and monitor users’ calls, violating their privacy rights. Same is the case with cloud computing, where a user’s privacy might be at risk, thus requiring appropriate measures by cloud computing providers to ensure privacy.
According to Vic Winkler, author of “Securing the Cloud: Cloud Computer Security Techniques and Tactics”, cloud service providers (CSPs) can give rise to complications when it comes to users’ privacy because of the virtual mechanisms and cloud storage involved. CSP processes and user data do not always reside on the same system or data center, resulting in legal problems regarding authority and control. Apart from that, there could also be an intentional or unintentional loss of data with CSPs.
Lastly, according to Strickland, a large number of clients demand more storage space, which means that a firm would require quite a lot of storage devices. Normally, cloud computing requires double the storage devices it needs for storing all user data: greater storage space means more information and the ability to recover inaccessible data through backup devices.
Despite its rapid growth, there are many unclear aspects of cloud computing: while using cloud computing, who owns the data, the user or the company that provides cloud services? Can a cloud provider restrict users’ access to data? These questions are still under consideration by various companies, law firms and universities, according to Strickland.





marshalljimster We could be curious and ask the way in which the cloud hontsig technology works. Well, using the simple terms, it operates using a bunch of multiple connected servers collaborating ( formed like clouds ) to host a bunch of web sites in contrast to the normal webhontsig service that utilises and relies on a single server.